Hi,
I cloned OSLC4J Bugzilla adapter project(GitHub - eclipse/lyo.docs: Lyo project repository (lyo.docs)) and followed the developer guide to config the project in my local.
When editing the bugzilla_uri ( src/main/resources/bugz.properties in the Lab6 project), I wanted to use this address https://landfill.bugzilla.org/bugzilla-2.18-branch/, and also I wanted to create my own account at Bugzilla Landfill, I found out I cannot access it and it shows this site can’t be reached.
Can anyone help me on this problem?
Hi Leon,
Mozilla closed the Landfill long time ago, due to spam if I recall it correctly. Please use my smarx008/bugzilla-dev-lyo Docker image of pre-configured Bugzilla instead (see GitHub - OSLC/lyo-adaptor-bugzilla: Bugzilla adaptor based on Eclipse Lyo for further details).
Cheers,
Andrew
Worth mentioning that it is also worth looking at the reference implementation if you are exploring to learn how to develop with Lyo and OSLC.
That’s a minimal install without email. Please read the README, it says:
Use admin:password as credentials to log in.
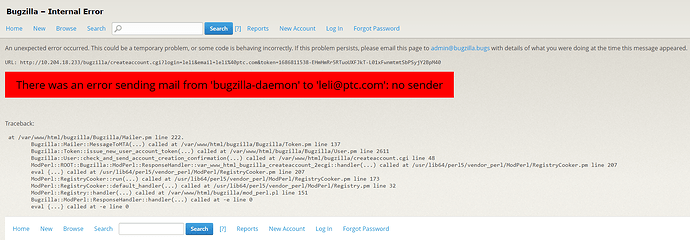
Thanks. I just run into another problem, the project I run in another test machine, as you can see I use the IP to visit instead of localhost. But when I use the name and password to login, it will return to localhost…
Should be possible to configure in adaptor-bugzilla/src/main/webapp/WEB-INF/web.xml
Hi Andrew, finally I can run the project in my local environment, thanks for your help.
But I still have one question want to ask you, I’m wondering which version of OAuth the lyo project uses, 1.0 or 2.0? If using v1.0, do you have any plans to upgrade to v2.0?
Great to hear that you got the sample code running, Leon!
Lyo provides support for OAuth 1.0a only at the moment. OSLC suggests to use OAuth 2.0 where possible (unfortunately, you cannot avoid 1.0a in many integrations involving IBM ELM/Jazz). The main reason Lyo has support to make it easy to add OAuth 1.0a is because OAuth 2.0 should require much less effort with an external provider like Keycloak, for example. See Chapter 16. Security and OAuth 2.0 | RESTful Java with JAX-RS 2.0 (Second Edition) for JAX-RS/Jersey related guidance.
If you would be kind enough to extend our sample with OAuth 2, we would be very happy to merge your pull request.
–Andrew.